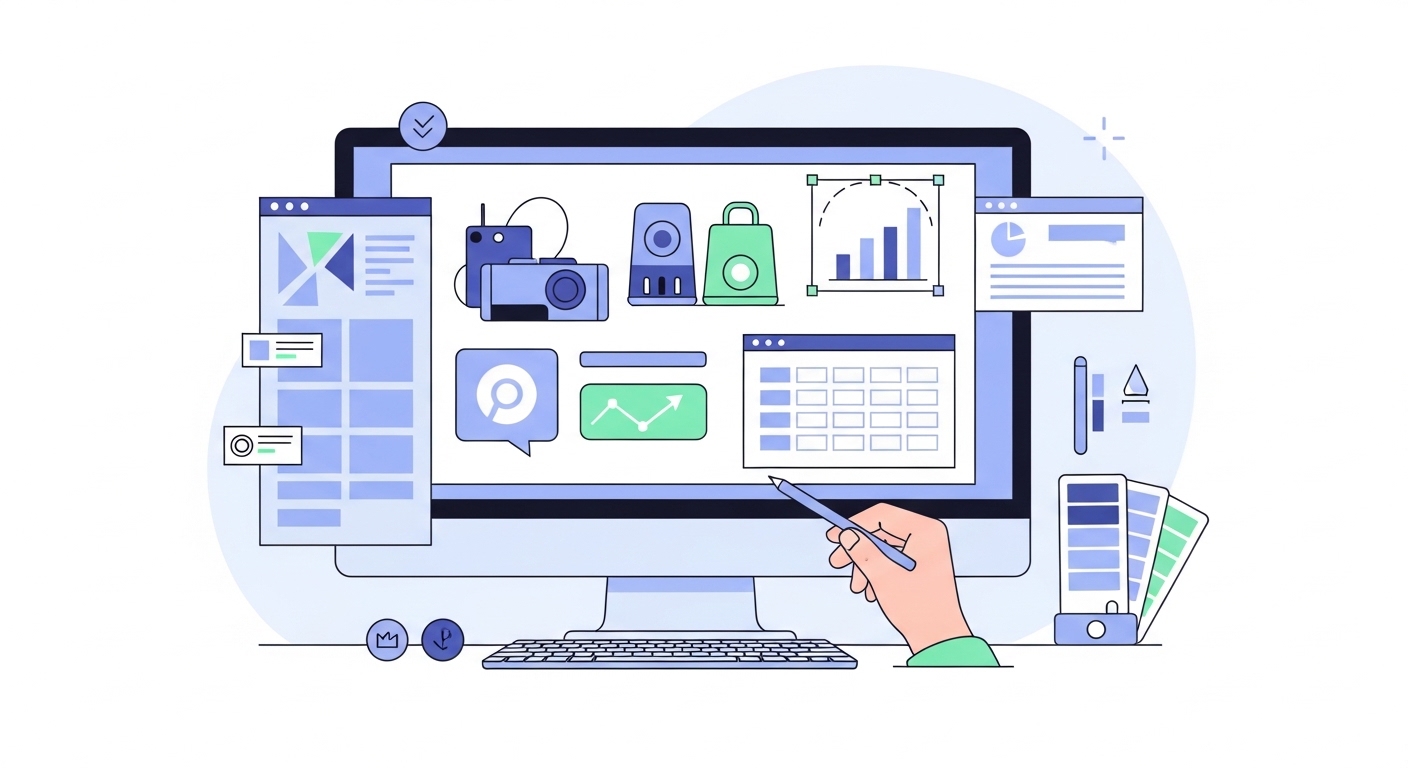
Information Security Video Production for B2B Growth
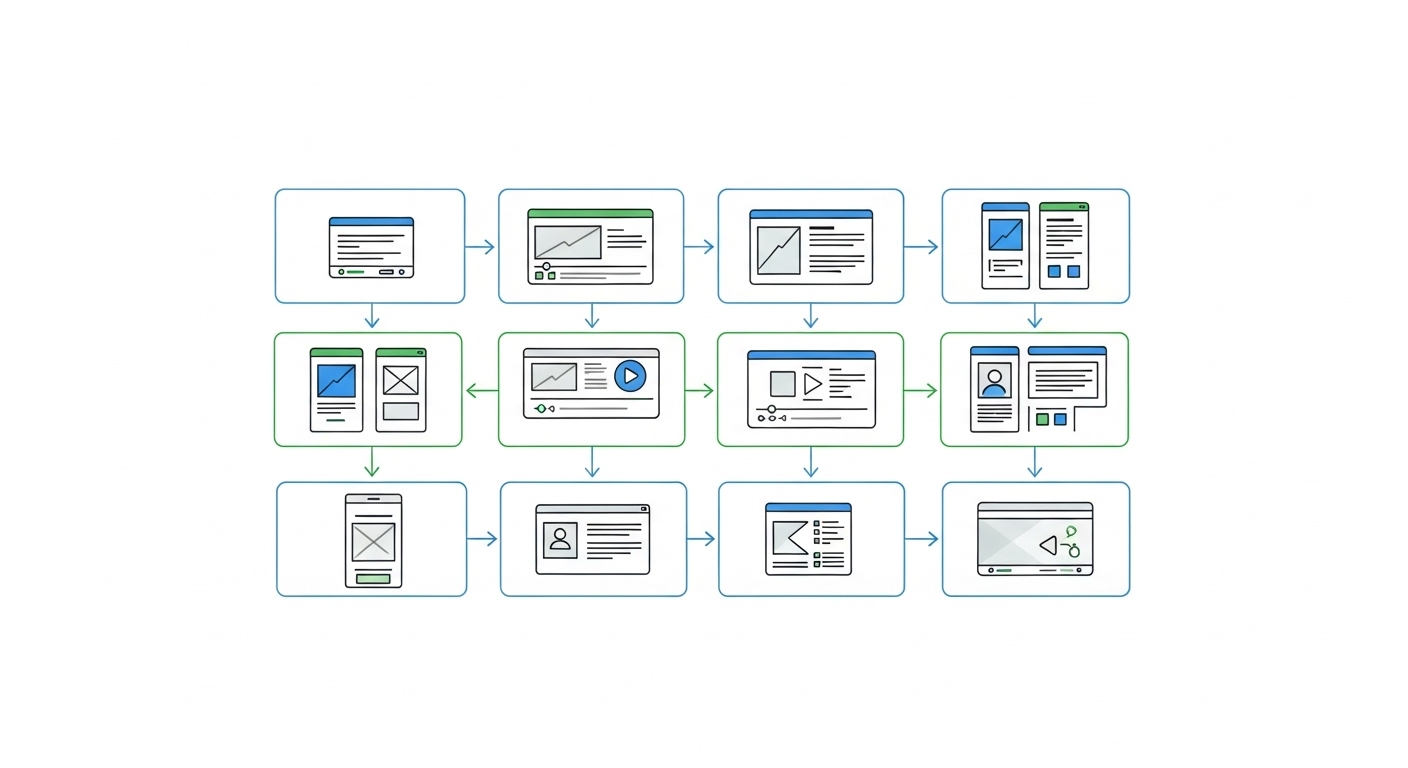
Our studio creates technical video content that simplifies complex security protocols for enterprise buyers. This production approach accelerates procurement by clarifying risk mitigation strategies and compliance standards.
Over 67 videos for Information Security Companies